When is the last time you said “wow” when you tried something new? Alright, the poke bowl you had yesterday sounds pretty great but I’m talking about technology here. When was the last time you tried something game-changing?
Hey, my name is Matt and I’m an Associate Dev Architect with the digital identity integration specialists here at WhoIAM. We build consumer identity solutions using technology like OpenID Connect, SAML, and Azure AD B2C.
Over the last couple of months, our team has been working with a new service from Microsoft’s identity team called Entra Verified ID that promises to fix problems like data residency and difficult federation that are common in our industry. Microsoft’s implementation of Verifiable Credentials is in its early stages – but very promising. It solves a variety of key use cases today for customers across industries, and is worth a look if you’d like to be at the bleeding edge of technology.
Beyond that bleeding edge is a world where we could have our cake and eat it too with online services being both secure and frictionless. To do that, Verifiable Credentials seeks to replace your username and password combo with a virtual, tamper-evident ID card that exists in an app much like a real-life wallet. This system has the potential to:
- Get rid of your giant book of passwords (or password manager library)
- Make it easy to verify credentials from another institution (like a university diploma) without a long and complicated integration process
- Allow in-person verification of online identities.
- For example, you register for an event that has invited certain organizations. To attend, you need to prove that you’re a member of the organization to get your badge.
- Without strong verification, anyone could photoshop a company badge. You could match on name and driver’s license, but the front desk would have to spend a lot of time doing that, creating long lines.
“Oh great another proprietary cloud service”
I would be rolling my eyes too, but Entra Verified ID seems to be doing a lot of things right.
1. Open Standards
It’s based on open standards from W3, the main web standards organization that has spec-ed out HTML, CSS, and HTTP just to name a few. Microsoft is one of many companies implementing this spec.
For now, Microsoft Authenticator is the only wallet you can use with Verified ID. However, there is a common spec being built that allows wallets to work with each other. You can see this in the URL scheme from the specification below:
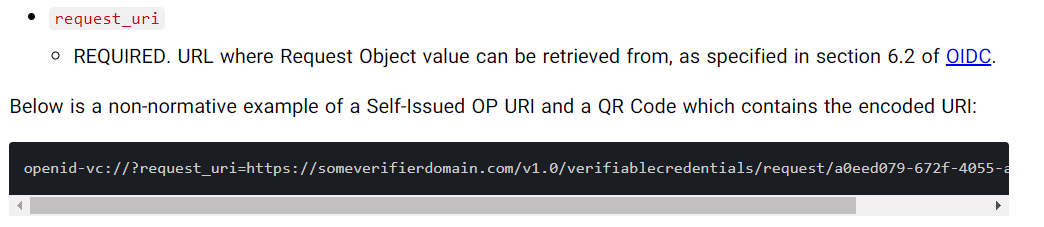
I’ve confirmed that both Microsoft and Auth0 are following this URL scheme. As of January 2, 2023, the wallets of the two companies almost worked together*, so the future looks promising. Other wallets to check out include Dock and Mattr.
2. Security
Each identity provider (IdP) represents a treasure trove of information and exploit potential. As an attacker, if you compromise a user’s password or breach the IdP, then you’re in. If you breach the IdP, then all users on that system are hosed since your passwords can get dumped (depending on how securely they were stored). See The National Institute of Standards and Technology’s (NIST) paper on IdPs for details: https://pages.nist.gov/800-63-3-Implementation-Resources/63C/IdP/
Sites like haveibeenpwned exist to check if your password has been compromised as part of a breach. If you enter your email, odds are that some service you use has been compromised. This directly relates to the push towards removing passwords in businesses.
3. Focus on end-user privacy and security
Verifiable Credentials seeks to eliminate the need to store your passwords and sensitive data on someone else’s server. Instead, you would store a credential that lives on your device. So, instead of the identity provider being the source of truth for “are you who you say you are”, you and your device are. The spec also allows for a couple of interesting privacy-preserving features. Say you have a student ID card that has your full name and ID number:
- Selective disclosure: a site giving student discounts can ask for just your full name for shipping info while the card itself proves that you’re a student. Other sites like an internal university site transcript would need to ask for your ID number to retrieve the transcript.
- Abstract claims: to prevent disclosing personally-identifiable information, an issuer (like an id verification service or government) could set an “ageOver21 = [true or false]” value on your card when issued. The user could then present this to a grocery store instead of their full birth date.
*Both of these features aren’t implemented yet in Entra Verified ID but are coming eventually.
4. Easier federation
Authentication and authorization have a steep learning curve for everyone, even seasoned developers
This is why working with Verifiable Credentials surprised me – the learning curve was way more intuitive because it works on a real-life analog: wallets.
You can issue a credential and present one, just like a driver’s license. The entity issuing the credential needs to be legitimate, but once issued, it goes straight to your wallet – a secure app on your phone. When presenting, the credential data gets directly sent to the site or app that needs it.
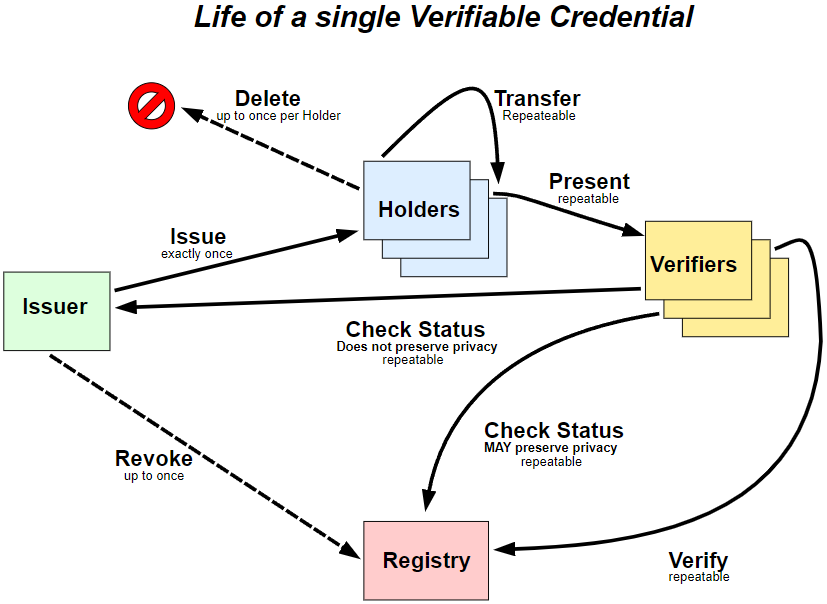
From w3c’s lifecycle details section in the data model spec
Notice something missing? That’s right, there’s no IdP required. That’s important for a couple of reasons:
5. Implementation Effort
Imagine you’re selling cactus juice online. All you need are the customer’s email, name, address, and payment details to complete an order. Guest accounts work fine for a while… but what if you want to implement a loyalty program? What if your customers want to see their order history? Then you start needing some sort of identity system.
With verifiable credentials, you could create a presentation request for just the info you need without the user needing to make an account with your company. For example, the issuer could be an identity verifier like ID.me, and you would be the verifier. Sure you could federate in from a provider like Google, but that still requires an identity system of your own. Federation also leaves another opening for attackers as shown in the Facebook/Spotify hack (which I have some personal experience with)
As someone who’s implemented a good amount of identity solutions for clients, the two reasons above already get me excited to keep working with this tech and seeing where it goes.
Wrap Up
Like any emerging technology, there’s a lot of work that needs to be done to make it easy to integrate and build on. Industry adoption is still underway and it’s going to be a while before everybody is using Verifiable Credentials instead of the usual username/password for everything.
Having said that, I’m very excited about the direction Microsoft’s Entra Verified ID and Verifiable Credentials as a whole are going in.
- W3C has a full roadmap that shows possible integration with WebAuthN eventually: https://w3c-ccg.github.io/roadmap/diagram.html
- Auth0’s Verifiable Credential launch made YCombinator’s Hacker News: https://news.ycombinator.com/item?id=33427503
- The UK’s National Health Service has started using Verified ID: https://customers.microsoft.com/en-us/story/1348169400682329017-nhs-foundation-trust-health-provider-m365
Resources:
- Learn about Entra Verified ID: https://learn.microsoft.com/en-us/azure/active-directory/verifiable-credentials/decentralized-identifier-overview
- Read through the official W3 Spec: https://www.w3.org/TR/vc-data-model/
- Check out the https://identity.foundation/ organization members to learn about all the players in this space (and I’m sure they’d love it if you subscribed to their newsletter)
Side Notes:
*: Auth0 didn’t offer scannable QR codes for credential issuance, so I had to try making a presentation request for an Auth0 credential on Verified ID I changed the issuer and accepted credential type and scanned the QR code with Auth0’s sample wallet app. I then got an error: “Property origins contains an invalid origin”. This could be worth investigating in a follow-up article.
Going the other way, I tried scanning an Auth0 presentation request without the credential in Microsoft authenticator, and managed to see the “domain verified” icon, which is a good sign.