Planning for Azure AD B2C End-of-Service
Microsoft has stated that Azure AD B2C is no longer available to purchase for new customers as of May 1, 2025, while existing customers can continue using the service. Microsoft has not published guidance on when Azure AD B2C will go out of support. However, that decision will be based on functional parity of Entra External ID with Azure AD B2C as well as the availability of robust tooling to migrate customers over to the new CIAM platform.
That runway is helpful – but migrations of CIAM platforms are rarely “lift-and-shift.” The work typically spans:
- Directory migration (profiles, custom attributes, identities)
- Credential strategy (password migration, recovery flows, risk controls)
- Experience migration (B2C user journeys and custom policies → External ID patterns)
- Application cutover (OIDC/OAuth settings, tokens, endpoints, sessions, phased rollout)
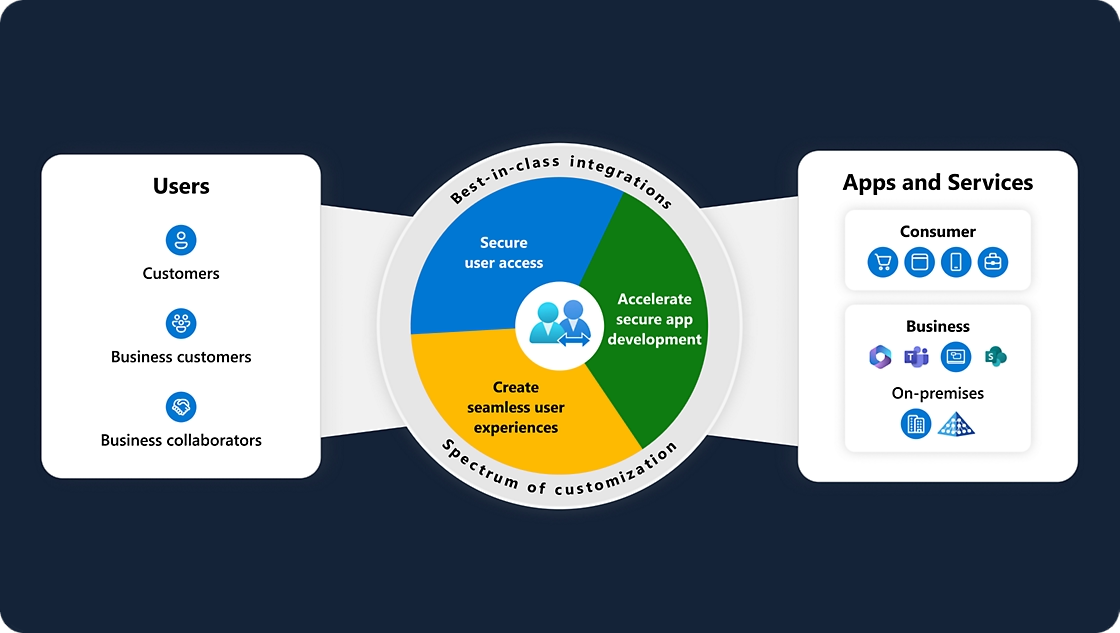
WhoIAM specializes in Azure AD B2C and Microsoft Entra External ID delivery, with a long track record building and operating CIAM at large scale.
How WhoIAM supports your migration
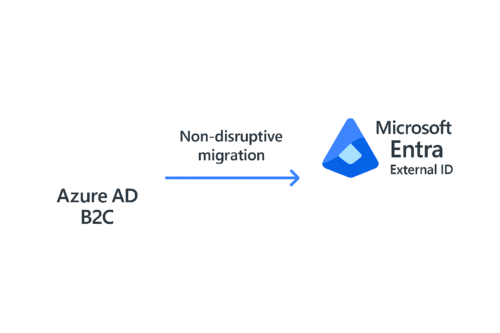
1) Just‑in‑Time (JIT) migration tooling for a non-disruptive transition
For most large consumer identity systems, the hardest part isn’t profile data—it’s passwords and minimizing user friction.
WhoIAM has built a Just‑in‑Time (JIT) user migration solution designed to seamlessly transition users from Azure AD B2C to Entra External ID with migration during authentication, using Microsoft Graph APIs and robust error handling.
This aligns with Microsoft’s documented approach where JIT password migration can be implemented to migrate credentials at sign-in via extensibility and a custom API—so the experience can be seamless from the user’s perspective.
What you get
- A proven JIT migration pattern to reduce customer disruption
- Guidance on coexistence strategies and cutover sequencing
- Secure integration design (Graph usage, app registrations, operational hardening)
2) Deep expertise migrating B2C user journeys & custom policies to External ID
If you’ve invested heavily in custom policies / user journeys, migration isn’t just configuration—it’s translation of your business logic.
WhoIAM has delivered engagements explicitly focused on re-implementing Azure AD B2C custom policy flows using Entra External Identities / External ID, including architecture planning and migration knowledge transfer.
Microsoft also acknowledges the industry reality: many customers have substantial custom policy investments, and the External ID platform is designed to simplify experiences (with migration paths evolving).
Typical focus areas
- Mapping B2C custom policies / IEF journeys to External ID user flows and extensibility
- Token/claims strategy and custom attributes mapping
- Recreating controls and ensuring parity where required (authentication methods, MFA posture, recovery flows)
3) Bulk pre‑migration at massive scale (millions to tens of millions)
Most enterprises can’t wait for “all users to log in” to move forward. You often need a bulk pre-migration baseline—then JIT migration for credentials and long-tail users.
WhoIAM offers tooling and delivery support for bulk user migration and has referenced a bulk user‑migration tool for consumer identities used by clients with millions of identities.
WhoIAM has also delivered CIAM programs operating at very large population sizes (including tens of millions of identities in production deployments).
What this enables
- Bulk import of profile data and attributes into External ID using Graph-based approaches (Microsoft’s recommended direction)
- A phased program where bulk pre‑migration reduces risk, and JIT handles credentials and late adopters
Our engagement model
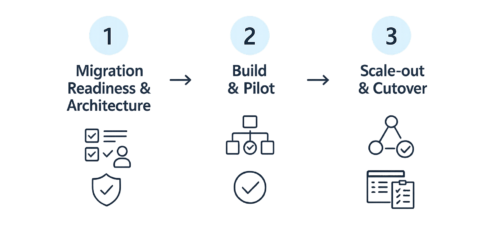
Step 1: Migration Readiness & Architecture (1–3 weeks)
We work with your engineering and security stakeholders to produce a concrete migration plan:
- Current-state inventory (tenants, apps, policies, identity providers)
- User/credential strategy (bulk + JIT + recovery options)
- Cutover approach (phased rollout vs. big-bang)
- Risk register and mitigations
Step 2: Build & Pilot (4–8 weeks)
- Stand up External ID tenant and core configuration
- Implement bulk pre-migration pipeline
- Implement JIT migration for credentials and sign-in continuity (when applicable)
- Pilot with one or two apps / cohorts
Step 3: Scale-out & Cutover (program timeline varies)
- Expand to remaining apps and user journeys
- Execute phased cutovers and monitoring
- Establish runbooks, operational dashboards, and post-cutover support
Outcomes you can expect
A clear, executable plan for migrating apps and users to External ID, with milestones and decision points.
A non-disruptive user strategy using a combination of bulk pre-migration and JIT migration.
Modernized identity experiences that move you away from brittle XML-heavy policy maintenance toward External ID’s supported patterns as they evolve.
FAQ
“Is Azure AD B2C going away?”
Microsoft states B2C is not available for new purchases and will be supported until at least May 2030 for existing customers. Even with that runway, teams are migrating now to avoid compressing risk into the final years and to align with the platform Microsoft is investing in.
“Can we migrate passwords without forcing resets?”
Microsoft documents a Just‑in‑Time password migration approach for External ID where credentials can be migrated at sign-in using extensibility and a custom API. WhoIAM also offers a JIT migration tool and services designed specifically for B2C → External ID transitions.
“We have complex B2C custom policies—can we keep them?”
External ID is designed to simplify the experience so custom policies are no longer required in the same way, and Microsoft has indicated migration paths will evolve. WhoIAM helps you translate your journeys and logic into External ID patterns and supported extensibility.
